1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
|
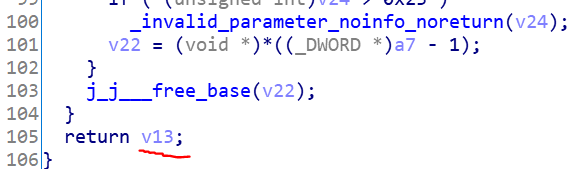
void __thiscall (HWND *this)
{
......
v21 = (CWnd *)this;
UserName_Text_ID = GetDlgItem(this[8], 1000);
memset(&UserName, 0, 02000u);
SendMessageA(UserName_Text_ID, 'r', 02000u, (LPARAM)&UserName);
RegCode_Text_ID = GetDlgItem(*((HWND *)v21 + 8), 1001);
memset(&RegCode, 0, 02000u);
SendMessageA(RegCode_Text_ID, 'r', 02000u, (LPARAM)&RegCode);
v3 = v21;
User_Choice = CWnd::GetDlgItem(v21, 1004);
v20 = SendMessageW(*((HWND *)User_Choice + 8), 0xF0u, 0, 0) == 1;
v21 = (CWnd *)&v14;
v19 = 15;
v18 = 0;
LOBYTE(v14) = 0;
if ( (_BYTE)RegCode )
v5 = strlen((const char *)&RegCode);
else
v5 = 0;
assign_sub_402A70(&v14, &RegCode, v5);
v49 = 0;
v13 = 15;
v12 = 0;
v8 = 0;
if ( (_BYTE)UserName )
v6 = strlen((const char *)&UserName);
else
v6 = 0;
assign_sub_402A70(&v8, &UserName, v6);
v49 = -1;
if ( sub_405510(*(LPVOID *)&v8, v9, v10, v11, v12, v13, v14, v15, v16, v17, v18, v19, v20) )
{
v24 = 'e R';
v40 = 0;
v7 = (wchar_t *)&v24;
v25 = 'i g';
v26 = 't s';
v27 = 'r e';
v28 = (int)&loc_53001D + 3;
v29 = 'c u';
v30 = 'e c'; // RegisterSuccess,Congratulation!
v31 = 's s';
v32 = &loc_43002C;
v33 = 'n o';
v34 = 'r g';
v35 = 't a';
v36 = 'l u';
v37 = 't a';
v38 = 'o i';
v39 = '! n';
}
else
{
*(_DWORD *)v41 = 'e R';
v7 = v41;
v42 = 'i g';
v43 = 't s';
v44 = 'r e'; // RegisterFailed
v45 = &loc_460020;
v46 = 'i a';
v47 = 'e l';
v48 = 'd';
}
CWnd::SetDlgItemTextW(v3, 1003, v7);
}
|





近期评论